Strengthening Security and Governance in the Cloud for Financial Services

The Challenge
With the company's consolidation in the market, the increase in the number of clients, and the prospect of growth, Norte Asset identified the need to strengthen its security mechanisms. It was essential to separate the development, testing, and production environments into separate AWS accounts, providing refined control in the lifecycle of internally developed solutions. Additionally, it was necessary to establish strict access control aligned with industry best practices.
Solution
CloudDog, introduced to Norte Asset by AWS, understood the complex context and identified the opportunity to enhance the company's management model. The proposed solution was developed based on the concept of infrastructure as code, utilizing AWS CloudFormation Control Tower (CfCT). This approach allowed for the implementation of the Landing Zones architecture, in conjunction with the Transit Gateway, aiming for efficient management of internal network traffic between environments and integration with partners.
Furthermore, the solution incorporated various AWS Security Services to ensure the protection of Norte Asset's resources. AWS Security Hub was adopted to centralize security management, while Amazon Inspector was implemented for early risk identification. Amazon GuardDuty was used for threat detection, and Amazon Detective for anomaly analysis.
All components of the solution, present in AWS accounts, generate audit logs that are stored in a segregated account, ensuring the integrity and immutability of these records. Additionally, a specific account was created for security auditors to analyze the security of the environment without having to access the accounts hosting workloads.
The network and IT infrastructure were enhanced through a dedicated account, including a replica of Active Directory and Amazon Workspaces. These solutions enable desktop virtualization and are used by analysts when they are outside the office, providing greater flexibility and productivity.
In application development, discipline was established through the use of a specific DevOps account. Programmers develop applications using the tools available in this account, and automations ensure the delivery of the final version directly to the appropriate environments, following the development pipeline structure.
The solution, developed with the concept of infrastructure as code using CfCT, provided Norte Asset with a consistent, scalable, and highly secure architecture in its AWS accounts. This approach not only met security and governance needs but also allowed for easy replication of the solution for other CloudDog clients who seek a similar level of management and security in their AWS accounts.
Architecture
The architecture implemented to meet Norte Asset's needs consists of different AWS accounts, each playing a specific role. Here is a description of the architecture and the respective accounts:
- Management Account: Responsible for managing and governing Norte Asset's infrastructure. In this account, the following services are configured: AWS Single Sign-On (SSO) to facilitate access to AWS resources, Amazon Organizations to manage account structure and policies, Amazon CloudTrail to record activities and audits, AWS Config to assess and track configuration compliance, AWS Control Tower to standardize and manage security best practices, and AWS Budgets to monitor expenses.
- Logs Account: Dedicated to storing and managing logs generated by the architecture's services. Amazon S3 is used in this account to securely and durably store logs.
- Audit Account: Focused on security and auditing Norte Asset's environments. In this account, AWS Security Hub, Amazon Detective, Amazon GuardDuty, Amazon Inspector, and Amazon Athena services are configured. AWS Security Hub centralizes security information and provides insights into potential risks and violations. Amazon Detective is used for anomaly analysis and investigation of potential threats. Amazon GuardDuty continuously detects threats and malicious activities. Amazon Inspector identifies security risks and vulnerabilities in advance. Amazon Athena is used to query logs stored in the Logs account, allowing efficient searches and analyses.
- IT Account: Responsible for network and information technology infrastructure. In this account, two Transit Gateways are configured: one to connect the São Paulo region, the local office, and the production environment, and the other to connect the development and testing environments in the Virginia region. These Transit Gateways facilitate secure and efficient traffic between environments while maintaining proper segregation. Additionally, the Amazon Workspaces service is included for desktop virtualization, providing greater flexibility and productivity for Norte Asset analysts.
- Production, Testing, and Development Accounts: Dedicated to environments related to Norte Asset's products, segregated according to the stages in the lifecycle. Each account has the necessary resources to support its respective environment, such as server instances, databases, and other relevant services. As can be seen in the diagram below:
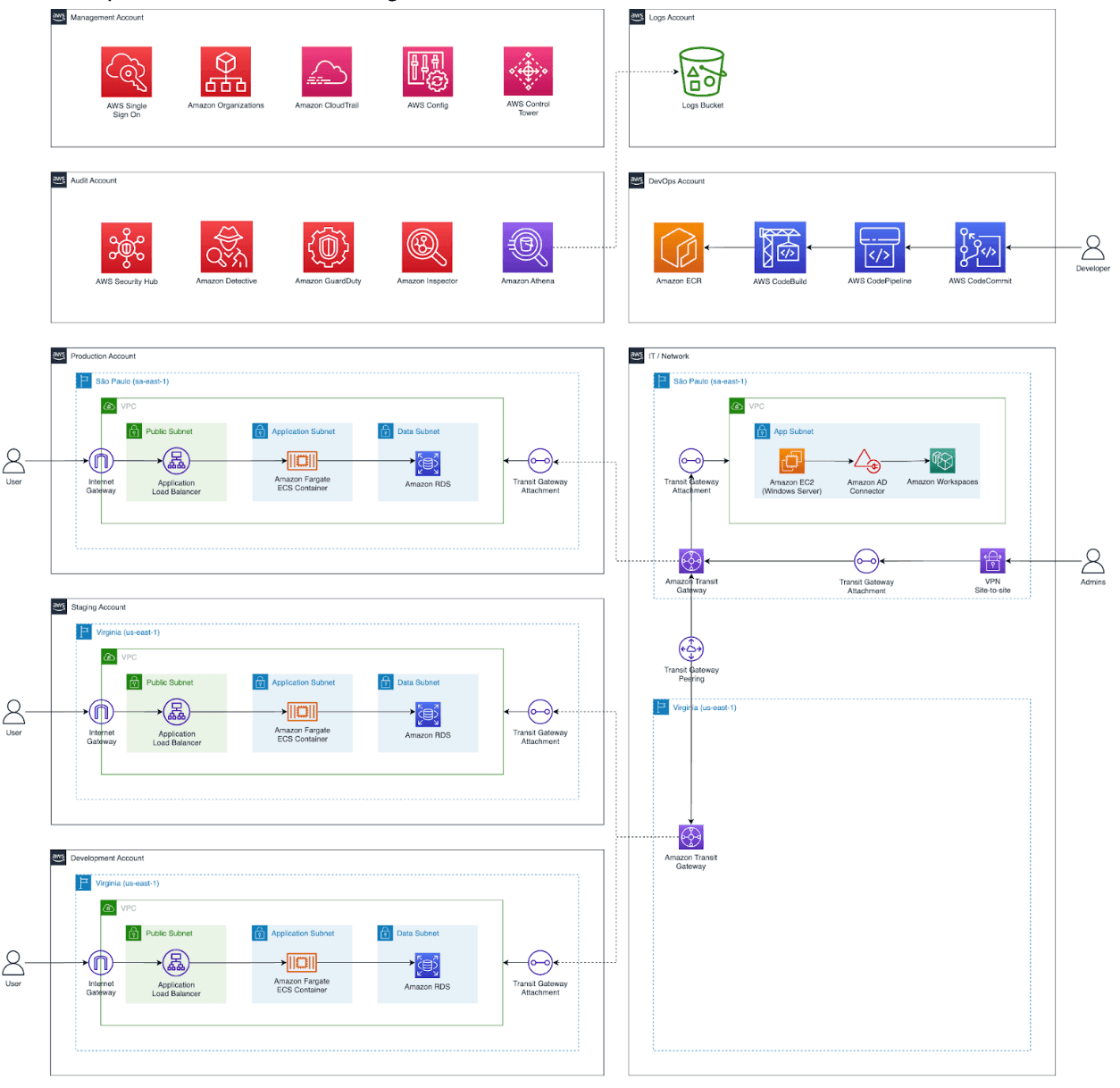
With this architecture, Norte Asset can efficiently manage its cloud resources, ensuring security, segregation, and proper control at each stage of its product lifecycle. This provides a reliable environment for development, testing, and production, meeting the demands of the financial market securely and scalably.
Results
The implementation of the proposed solution yielded the following outcomes for Norte Asset:
- Strengthened security mechanisms: Achieved through the proper separation of development, testing, and production environments into distinct AWS accounts. Strict access control: Implemented in accordance with industry best practices, ensuring a high level of security.
- Advanced management of internal network traffic: Ensuring the security and efficiency of communications between environments and partners.
- Centralized security management: Facilitating early risk identification, threat detection, and anomaly analysis.
- Secure storage of audit logs: Stored in a manner inaccessible to internal personnel, strengthening transparency and the ability to detect security issues. Enhanced network and IT infrastructure: Including a replica of Active Directory and Amazon Workspaces for desktop virtualization, offering analysts greater flexibility.
- Disciplined application development: Employing efficient automations and direct delivery to appropriate environments, increasing the efficiency and quality of the development process.
These results not only met Norte Asset's security and governance needs but also contributed to a more efficient and transparent operation throughout all phases of their product lifecycle.
