Scaling SaaS Applications using Zero Sharing Architecture



The Challenge
OpsFactor faced several challenges regarding the management of its SaaS system, which has the characteristic of "shared nothing," where each customer has a separate environment for network and data segregation, allowing the definition of custom IP ranges and secure integration through site-to-site VPN.
In the previous architecture, the system used an EC2 infrastructure to host the Spring Boot application and an RDS to host the SQL database. However, as the customer base grew, managing multiple environments became challenging for OpsFactor's lean development and operations team.
They also faced challenges with enterprise customers, who had different processes for certifying new versions of the system. These processes required individualized rollout of updates for each customer.
Given this scenario, the company was looking for a solution that would simplify SaaS management while maintaining the zero-sharing characteristic, improving availability, and enhancing governance control. The need to manage and update various individual environments for each customer while ensuring security, scalability, and compliance was a significant challenge.
The Solution
CloudDog deployed AWS Control Tower to enhance the management of each client's accounts, advised on externalizing environment variables to enable application containerization using Docker, and separated transactional and batch processes, integrating them through an SQS messaging system.
Furthermore, they used CodePipeline and CodeBuild to build application images and make them available in a centralized container using the Elastic Container Registry.
They utilized AWS Service Catalog to organize infrastructure templates, allowing for infrastructure customization according to each client's individual needs in an automated manner lengthy sentence. This simplified the SaaS management while enabling cost separation, access management, security, and compliance.
Architecture
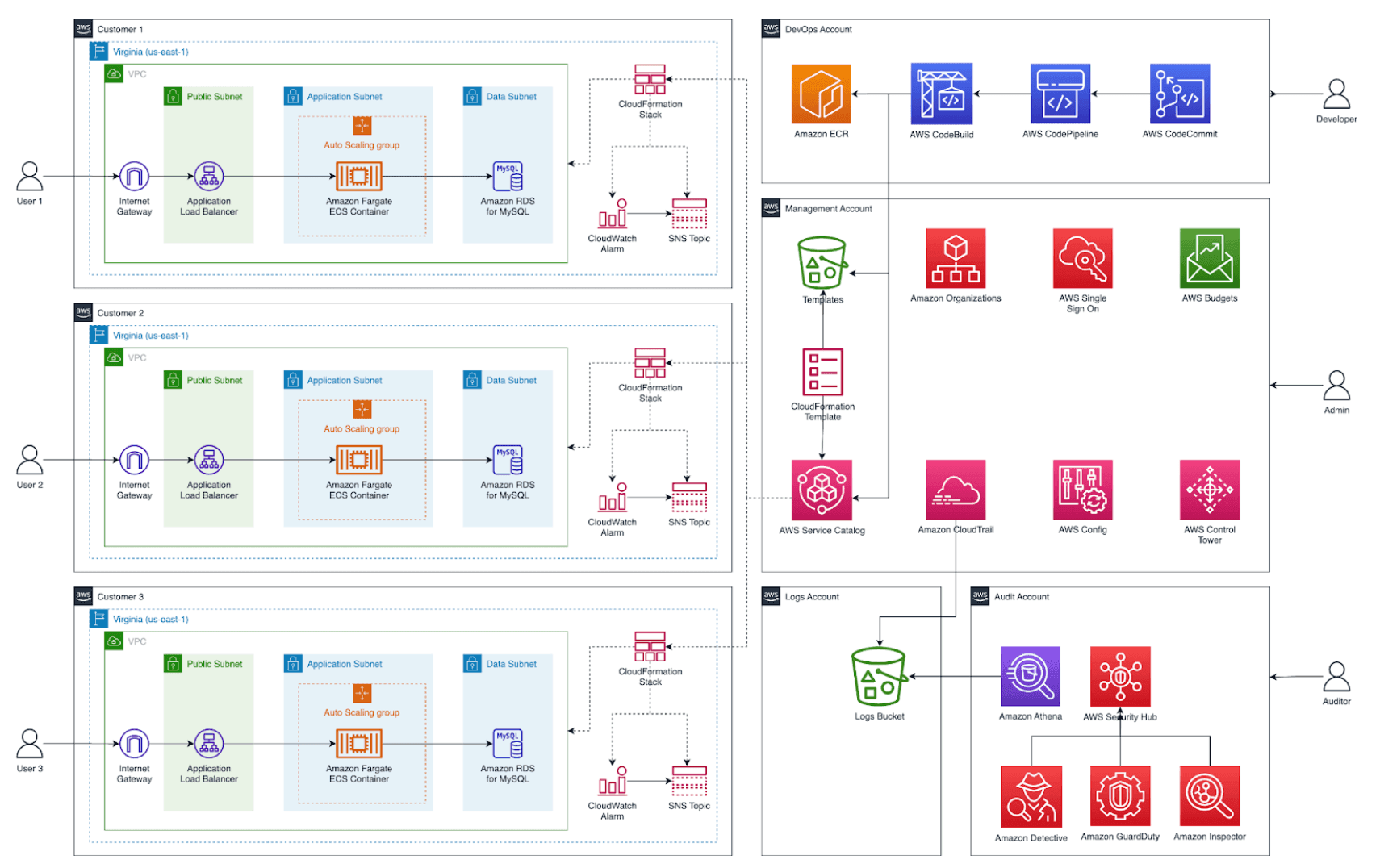
The architecture implemented to meet OpsFactor's needs involves different AWS accounts, each with a specific role. Here is a description of the architecture and the respective accounts:
- Management Account: Responsible for managing and governing OpsFactor's infrastructure. This account uses services like AWS Single Sign-On (SSO) for easy resource access, Amazon Organizations to manage account structure and policies, Amazon CloudTrail for activity logging and auditing, AWS Config to assess and track configuration compliance, AWS Control Tower to standardize and manage security best practices, and AWS Budgets to monitor expenses.
- Logs Account: Dedicated to storing and managing logs generated by the architecture's services. In this account, Amazon S3 is used to securely and durably store logs.
- Audit Account: Focused on security and auditing OpsFactor's environments. This account configures services like AWS Security Hub, Amazon Detective, Amazon GuardDuty, Amazon Inspector, and Amazon Athena. AWS Security Hub centralizes security information and provides insights into potential risks and breaches. Amazon Detective is used for anomaly analysis and threat investigation. Amazon GuardDuty continuously detects threats and malicious activities. Amazon Inspector identifies security risks and vulnerabilities in advance. Amazon Athena is used to query logs stored in the Logs Account, enabling efficient searches and analysis.
- Customer Accounts: Dedicated to the environments related to each OpsFactor client. In these accounts, all infrastructure is created and maintained, including VPC, RDS Database, ECS Containers, Load Balancer, CloudWatch Dashboards, and Alarms. Environments are configured from Service Catalog templates, allowing standardized and customized deployment for each client.
This architecture provides proper resource and data segregation among OpsFactor's clients, ensuring the necessary security, compliance, and scalability. By using separate accounts and specific services, the company can efficiently manage every aspect of the infrastructure and deliver a quality service to its clients.
Results
The results of CloudDog's implementation of the proposed architecture for OpsFactor include:
- Improved SaaS Management: The deployment of AWS Control Tower allowed for better management of each client's accounts, ensuring greater security and cost separation. This facilitated access management, security, and compliance.
- Higher Availability: The use of Docker containers and the separation of transactional and batch processes, integrated through the SQS messaging system, contributed to increased system availability. The architecture with separate accounts prevents issues in one environment from affecting others.
- Automation of CI/CD Process: The use of CodePipeline and CodeBuild streamlined the building of application images, simplifying the deployment process for clients, with application images made available and managed through AWS Service Catalog.
- Deployment of New Versions: Through AWS Service Catalog, OpsFactor gained more precise control over the deployment of software updates for its clients, as they can now schedule the application of new system versions on a date and time agreed upon with each client, avoiding unwanted interruptions in client processes.
These results provided OpsFactor with better SaaS management, increased system availability, enhanced governance control, and a simplified deployment process. With a lean team, the company was able to efficiently tackle the challenges of maintaining and evolving individual environments, meeting client needs, and promoting business growth.
